
We are thrilled to announce that Aserto now supports Azure Active Directory (Azure AD) as an identity provider! Azure AD is one of the most popular cloud identity providers on the market, which you can now use seamlessly with Aserto. You can use Aserto to write and enforce fine-grained authorization policies that use Azure AD users and groups as their targets.
This integration simplifies the process of managing access control for Azure AD customers. It does so by connecting the identities in Azure AD with the entitlements in Aserto. It also helps ensure that access control rules remain up to date with organization policy.
You can continue to leverage Azure AD to manage user identities and groups. You can then use Aserto to use that information to define fine-grained access controls, determining who has access to what resources.
Under the hood of the Azure AD integration
As organizations increasingly adopt cloud-based solutions, the need for efficient and secure identity and access management becomes more critical than ever. Aserto helps organizations add fine-grained, policy-based, real-time access control to their cloud applications.
Azure AD is the source of truth for users and groups for many organizations. It supports a broad range of authentication protocols, including SAML, OpenID Connect, and OAuth2. As a result, it enables customers to simplify their login process and improve their user experience with single-sign on.
Aserto picks up where Azure AD leaves off. It enables organizations to define fine-grained policies that control access to their resources. It also future-proofs applications by providing support for every authorization model, so organizations can easily evolve their model as requirements change.
When integrated, users and groups from Azure AD are imported into the Aserto graph-based directory. In addition to built-in support for users and groups, the directory offers a fully customizable schema for describing object types and relations based on an application’s domain model. It also supports OPA policies and lets you custom tailor policy to application through a set of Rego built-ins. As a result, you can combine RBAC, ABAC, and ReBAC, using identity information from Azure AD, along with application domain-specific object types, roles, and permissions.
And if you need to authorize multiple applications or services, we've got your back. The Aserto control plane provides centralized management of policies and data. It helps improve your security and compliance posture, while reducing complexity.
Authorization decision logs
The story doesn't end once a user is authenticated and authorized. For most modern organizations, audit trails have evolved from a nice-to-have feature to must-haves to facilitate compliance and forensics efforts.
Azure AD provides audit trails for user logins, capturing which user logged in when. Aserto builds on this capability by capturing and aggregating detailed decision logs for every access control decision. This enables users to go beyond login trails and track who accessed what resources and when. It also provides context into why access was granted or denied.
Conclusion
The Aserto integration with Azure AD is yet another step in our commitment to provide a flexible and secure authorization platform. We are excited to offer Azure Active Directory users a seamless connection with our authorization platform. They can now target users and groups from Azure AD in authorization policies and enforce fine-grained controls with Aserto. They can also manage all their policies in one place, which simplifies policy management.
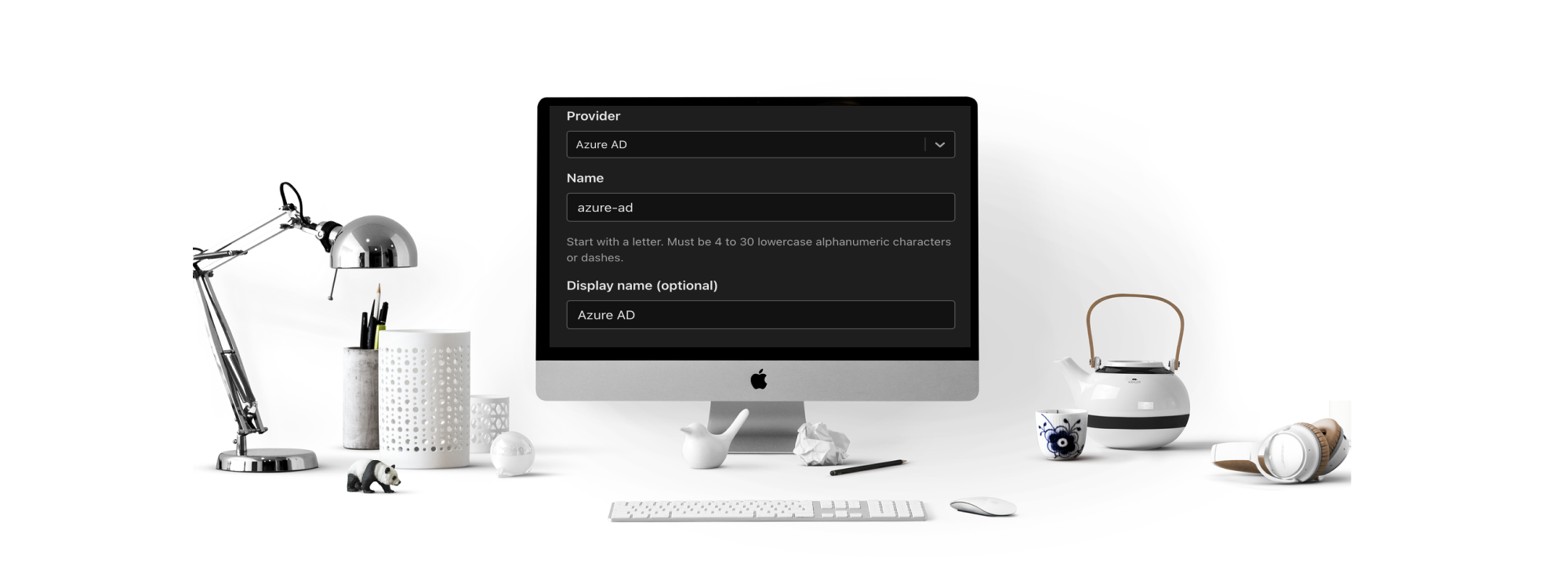
To get started with the integration, create a free Aserto account, and refer to the documentation on how to connect Aserto to your Azure Active Directory tenant.
As always, we'd love to hear your thoughts! Feel free to drop us a line with any questions or feedback you might have, or join our community Slack.
Related Content

Building a React and Node app with Aserto authorization
Adding an authorization layer to your React.js and Node.js application has never been easier! Learn how to create a role-based access control policy and how to use it to make authorization decisions in your application.
Apr 12th, 2023

Building RBAC in Go
If you're looking to implement RBAC with Go, there are several options to choose from. In this post, we'll review some of the existing tools in the Go ecosystem.
Aug 12th, 2024

Adding Authorization to a Go app with Topaz
In this tutorial, we'll learn how to add authorization to a Todo app written in Go, using the Aserto Go SDK.
Aug 20th, 2024
&color=rgb(100%2C100%2C100)&link=https%3A%2F%2Fgithub.com%2Faserto-dev%2Ftopaz)


