Fine-grained, scalable authorization in minutes
Resource-level access controls for any application, managed centrally and evaluated instantly.
Fast

~1ms authorizations
Flexible

Any model, any cloud
Easy

Get started in <5 minutes
Watch a 2-minute video
Granular permissions, live in minutes
Use our SDKs, quickstarts, and sample apps to easily integrate the Aserto fine-grained authorization platform.
Roles, hierarchies, subscriptions, sharing & collaboration, ready-to-go in minutes.






Real-time authorization
Eliminate standing permissions. Enforce in milliseconds, based on real-time data.
Deploy local authorizers to the edge of your application and let Aserto do the rest. The Aserto control plane will sync changes to authorization data with them in real-time to ensure you never authorize over stale data.
Central control
Manage all of your users, policies, authorizers, and authorization data from one place.
The Aserto control plane makes understanding authorization logic and managing access across applications as easy as pie.
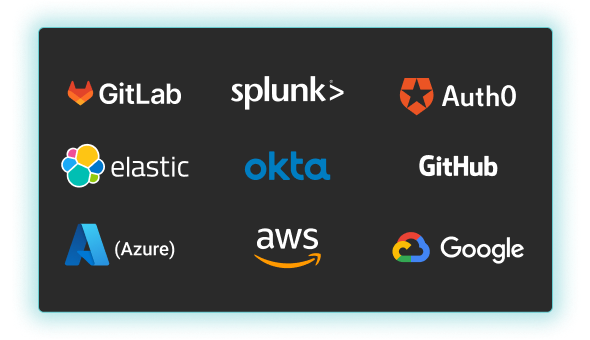
Works with what you have
Seamlessly add authorization to any application using our complete set of SDKs middleware, or using our gRPC / REST APIs. Then connect your identity provider, user directory, and SIEM tools using our pre-build integration.
Zero trust and least privilege by default
There is no zero trust without fine-grained access controls. Ensure users can only access what they need to at the moment, and easily change that logic, or what they can access.
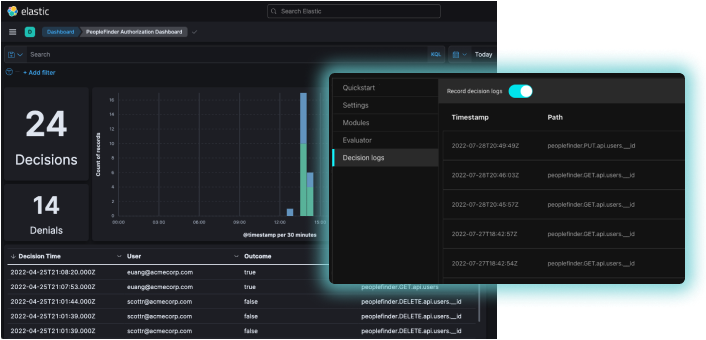
Compliance without the headache
Aserto automatically collects and aggregates authorization decisions along with all of the inputs, so you have complete audit trails. You can even map decisions to policy versions and the data that was used.
Cloud-native and open source
Aserto is based on a modern, cloud-native, open-source foundation, including the Topaz open-source authorizer, Open Policy Agent decision engine, and a Google Zanzibar inspired directory.

Don't build undifferentiated plumbing
Authorization is complex
Evaluating policy against real-time user attributes with millisecond latency and 100% availability is a distributed systems problem. Most engineering teams can’t justify taking the time to fully solve it.
Requirements constantly evolve
Custom roles. Custom attributes. Integration with enterprise identity providers and directories. Decision logs. ISO 27001. As products move up-market, teams that build them can't keep up.
You could be building customer value
"I want to rewrite RBAC!" said no engineer, ever. Your team could be working on end-user features instead of undifferentiated heavy lifting.
Built by developers, for developers



Join our slack
Discuss authorization patterns, get answers, and engage with our community.

Sign up for our newsletter
Get the latest technology articles and company updates in your inbox.
&color=rgb(100%2C100%2C100)&link=https%3A%2F%2Fgithub.com%2Faserto-dev%2Ftopaz)