Fine-grained relationship-based access control
Define and enforce roles and permissions based on relationships between your users and groups and your application's resource hierarchy



Fine-grained access based on resource relationships
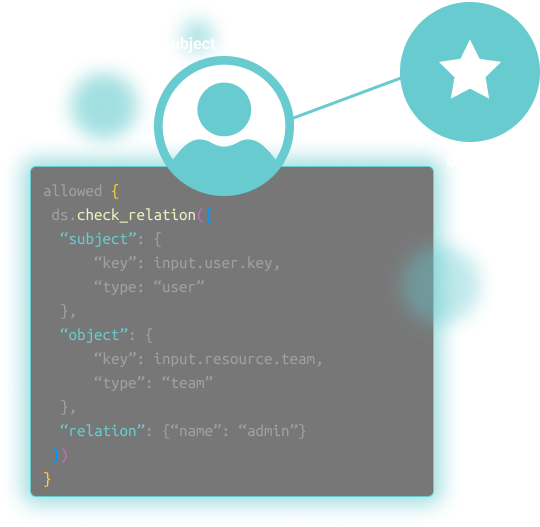
Relationship-Based Access Control (ReBAC) is a new take on the Access Control List (ACL) paradigm of cascading access to each resource in a hierarchy, such as directories and files. ReBAC generalizes this model into a relationship graph between subjects and objects via relations. ReBAC models can be traversed as a graph to determine whether a user or group has a certain permission on a resource.
Aserto’s Directory is built around the ReBAC model, and makes it easy to define a custom resource hierarchy that matches your domain model: organizations, teams, projects, lists, folders, and so on. You also define the set of relations - owner, admin, member, viewer - that relate these objects to subjects (users and groups). Aserto makes it easy to implement relationship based access control policies based on your application's unique domain model.

Control access to every level of your resource hierarchy
Define and enforce access control policies based on the relationships subjects have to resources in your system, as well as role and group information.

Combine ReBAC and ABAC rules in a single authorization policy
Use the best of both worlds, and combine relationship-based rules with user or resource attributes in a single policy.

Enforce in milliseconds based on real-time data
Resources and their relationships are synced to the policy decision point in your cloud automatically and in real-time to eliminate the risk of access based on stale data.

Control what your users can see and do
Influence frontend behavior as well as backend logic based on the relationship the end user has with the resource in question.

Define and manage policies in one place
Decouple policy from application code, allowing both security and engineering to move faster. Manage all of your policies and decision logs centrally to simplify governance and compliance.

Leverage the best of the open cloud native ecosystem
Aserto is built upon an open, cloud-native foundation, which includes Open Policy Agent (OPA), Topaz authorizer, Policy CLI, and many of the ideas in the Google Zanzibar system.
Explore popular authorization use cases
&color=rgb(100%2C100%2C100)&link=https%3A%2F%2Fgithub.com%2Faserto-dev%2Ftopaz)