GitLab Integration is here!
Apr 21st, 2022

Roie Schwaber-Cohen
Engineering

Today we’re happy to announce that Aserto supports GitLab as a source-code provider! You can now use both GitHub and GitLab to store and version your authorization policy code.
In order to add GitLab as a source-code provider, you first need to create a GitLab Personal Access Token.
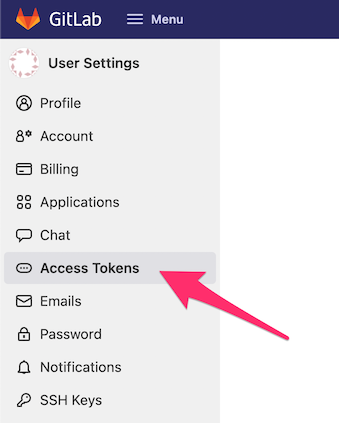
Log in to your GitLab account, and navigate to the personal access token page.
Name your token “Aserto” and assign it with an expiration date. Then, select the “api” scope:
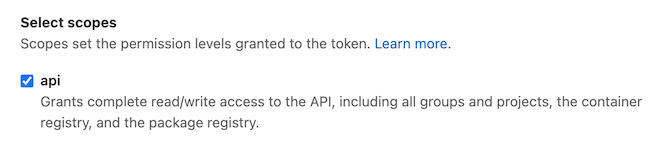
Finally, click “Create personal access token”:
Copy the newly created token, head to the Aserto console, and navigate to the Connections tab.
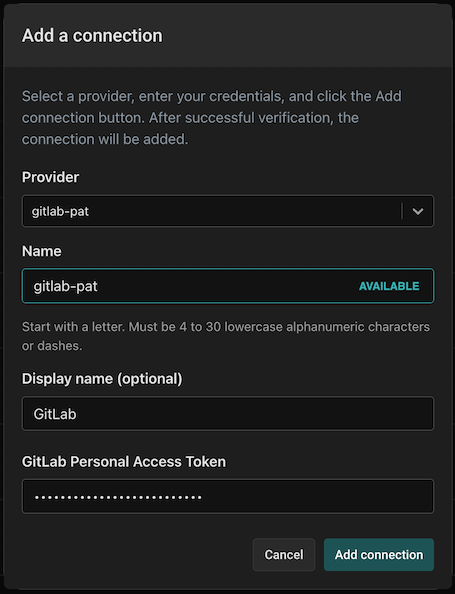
Click on “Add a connection”:

In the dialog, select the “gitlab-pat” provider and name your connection “gitlab-pat”. Use the display name “GitLab” and paste the newly created GitLab PAT. Finally, click “Add connection”.
To test the newly created connection, head to the “Registry” tab and click “Create a new repository”:
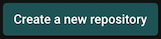
Select the “Use a template…” option and click “Continue”.
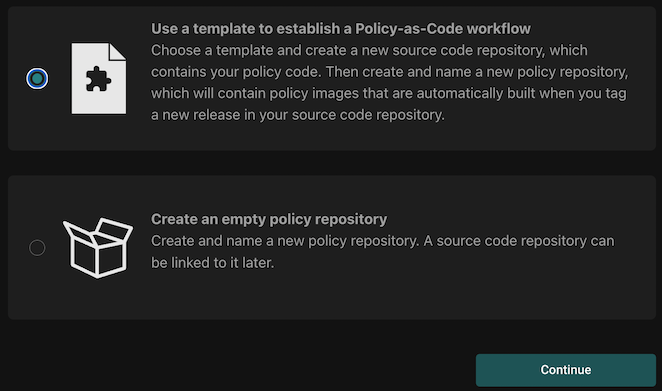
Select the source code provider GitLab:
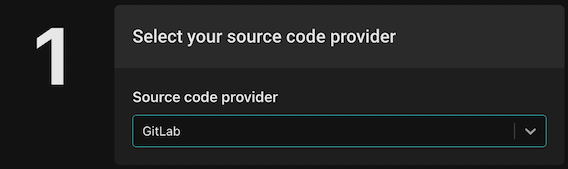
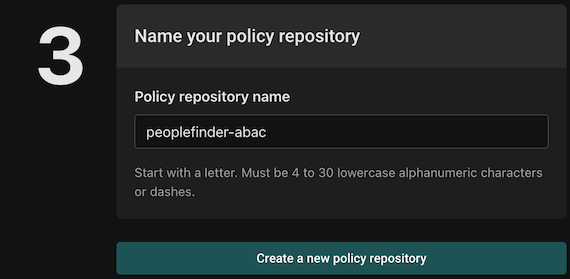
Next, select the `policy-peoplefinder-abac` template and select your GitLab organization. Name your policy repository `policy-peoplefinder-abac`.
Finally, name the policy repository `peoplefinder-abac` (this will be the name used for your policy repository in Aserto) and click “Create a new policy repository”.
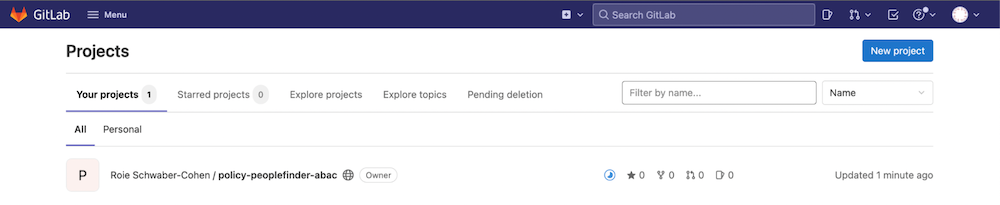
To view the newly created repository, head back to GitLab:
Aserto automatically creates the pipeline that builds the repository and pushes it to the Aserto image registry.
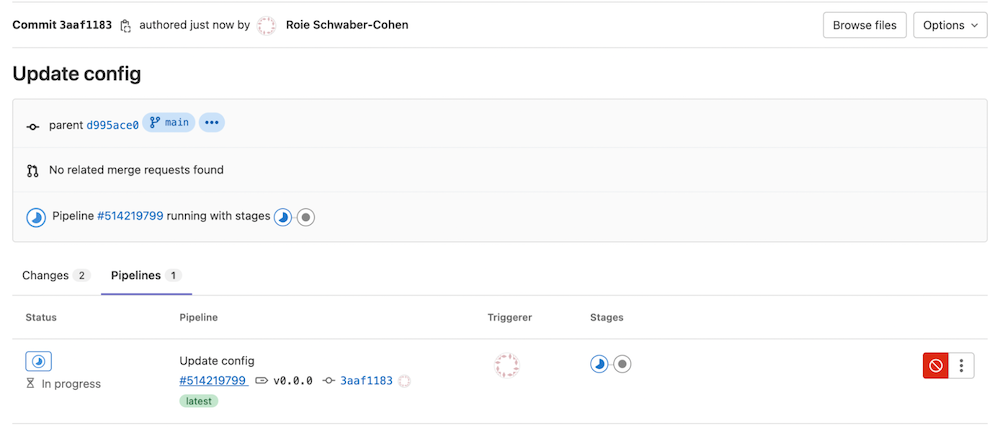
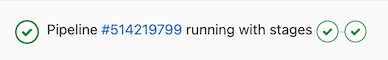
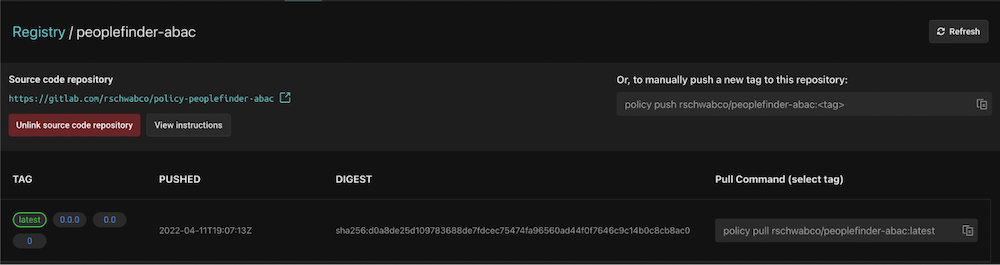
Once the pipeline is completed, you’ll see the following:
When you head back to the Aserto console, open the policy repository. You’ll see the following:
When you make changes to the policy and push them to the repository, the pipeline will run again and the policy will be automatically updated in the Aserto policy repository.

Roie Schwaber-Cohen
Developer Advocate
Related Content
Feature Review: Decision Logging
Aserto can collect and manage decision information from all your authorizers, including sidecar and other kinds of locally deployed ones. In this post, we will give an example of how to tap into the data generated by Aserto’s decision logging.
May 5th, 2022
Policy-as-Code for Docker and Kubernetes with Conftest or Gatekeeper
In this post, we'll explore how Aserto uses Policy-as-Code to centrally define our important engineering best practices and share them amongst a diverse set of teams and microservices.
May 12th, 2022
OPA natively consumers OCI images
OPA can now consume policy bundles packaged as OCI images. Used together with the Policy CLI, you can build, tag, push, and pull policies just like docker images.
May 18th, 2022
&color=rgb(100%2C100%2C100)&link=https%3A%2F%2Fgithub.com%2Faserto-dev%2Ftopaz)