Authorization service for Okta

Enterprise-grade authorization for Okta
About the integration
Okta is a comprehensive and customizable one-stop identity solution. Aserto is a powerful authorization service that enables you to define and evolve permissions and access within your application. Together, they provide out-of-the-box solutions for user identity and access management.
About Okta
Okta is a secure identity cloud that links all your apps, logins, and devices into a unified digital fabric. With Okta, you’re up and running on day one, with every app and program you use to work, instantly available.
Okta is built to cover a broad range of identity use cases quickly by combining pre-made components. Customers can customize their solution to their business needs with no-code, low-code, or pro-code options. This flexibility makes it easy to connect third-party apps and systems to Okta in order to enhance application security and user experience.
About Aserto
Aserto is a powerful and flexible authorization-as-a-service built to evolve with your customer requirements. It is complementary to Okta’s Identity solution: making it easy to define, enforce, and evolve permissions within the application. With its open-source authorizer, Aserto handles all the heavy lifting required to build secure, scalable, role (RBAC), attribute (ABAC), policy (PBAC), and relationship-based access controls (ReBAC).
Aserto integrates natively with Okta, and can be onboarded in under a day. Quickstarts and SDKs are available for popular programming languages and frameworks, including Node.js, Golang, Python, JavaScript, Ruby, Java, ASP.Net, and React, helping you get up and running in little to no time. REST, gRPC, and GraphQL APIs are available for developers that want to code close to the.
Better together
Setting things up
To get your authorization up and running, connect Aserto to your Okta tenant and then users, roles, and attributes stored in Okta will automatically sync with the Aserto directory. Inside Aserto you’ll define your permissions, and authorization policies, as well as load any resource contexts you’ll want to use in your authorization decisions.
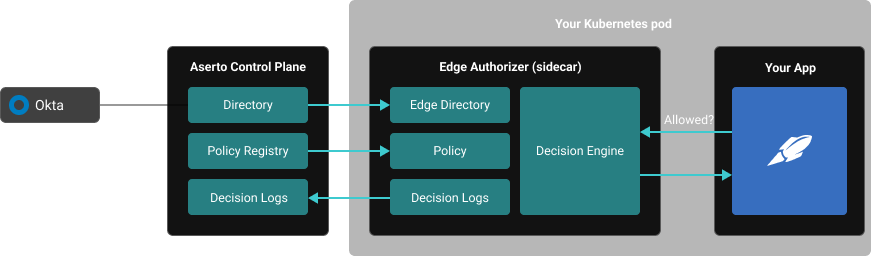
Start by testing against Aserto’s hosted authorizer, which Aserto operates for you. When you’re ready to run a production workload, deploy Aserto’s Authorizer as a microservice or sidecar in the same cluster or subnet as your application. The Aserto control plane automatically pushes the most recent user, resource, and policy data to all authorizers, so you never make decisions based on stale data.
At runtime
At runtime, Okta will send your application a signed access token once it authenticates a user. Before accessing a resource within your app, it should make a call to the Aserto authorizer. The user context, policy context, and resource context are fed to the authorizer by your application to inform authorization decisions. The Aserto authorizer uses the OPA decision engine to quickly make an authorization decision based on that data, which will be used by the application to gate unauthorized requests.
Auditing authorization decisions
Aserto captures logs of every authorization decision in the control plane as a decision log for easy auditing. Decision logs can be streamed or batched up into your favorite log analysis tool.
The Authorizer architecture
Authentication happens once per session, and authorization happens upon every request, so the speed of response is critical. To minimize authorization latency and maximize availability the Aserto authorizers are deployed as microservices or sidecars right next to your application. Your production application should never be dependent on the availability / uptime of a remote authorization service.
The authorizers make authorization decisions based on three important inputs:
1. Policies from your policy registry
2. Users, attributes, and roles from Okta supplemented with application-specific information stored in the Aserto directory
3. Resource context passed by in your application
Any changes made to your Okta directory are automatically synchronized into the Aserto directory, and Aserto then pushes updates to your authorizer in near real-time or can be configured to update on an interval determined by the application administrator.
Leveraging the policy, user, and resource contexts, Aserto makes it easy to evolve your authorization from coarse-grained RBAC to fine-grained authorization using attributes (ABAC), relationship-based access controls (ReBAC), or combinations. This means you can build a strong authorization foundation once, and evolve your access control model easily over time.
Integrating Okta with Aserto allows you to bridge the gap between authentication and authorization creating an end-to-end Auth solution.
Aserto also comes with the following benefits:
- Out-of-the-box support for audit trails, custom roles, RBAC, ABAC, and ReBAC
- Open-source authorizer you can deploy in your cloud today
- Use a policy-as-code workflow to build, tag, push, version, and pull policy images just like docker images
- Quick onboarding via first-class citizen integrations with Auth0 and your artifact registry, logging system, backend programming language, and frontend framework.
- Built on top of a trusted open source policy engine, the Open Policy Agent (OPA)
Resources
- Developer docs for connecting Okta to Aserto
- Developer guide to adding authorization to Okta apps (coming soon)
- Aserto demo for apps with identity providers
- Aserto authorization platform benefits
- OAuth2 scopes are NOT permissions
- Authentication != Authorization
&color=rgb(100%2C100%2C100)&link=https%3A%2F%2Fgithub.com%2Faserto-dev%2Ftopaz)