Aserto Console: June 2022 release notes
Jun 2nd, 2022

Piotr Puszkiewicz

Roie Schwaber-Cohen
Engineering
Our team has been hard at work making the experience of interacting with Aserto easier and more intuitive. Here are the changes we’ve made to the Aserto Console in our latest release:
Getting started
Aserto's console now presents new users with a "Getting Started" tab that helps them become familiar with key features.
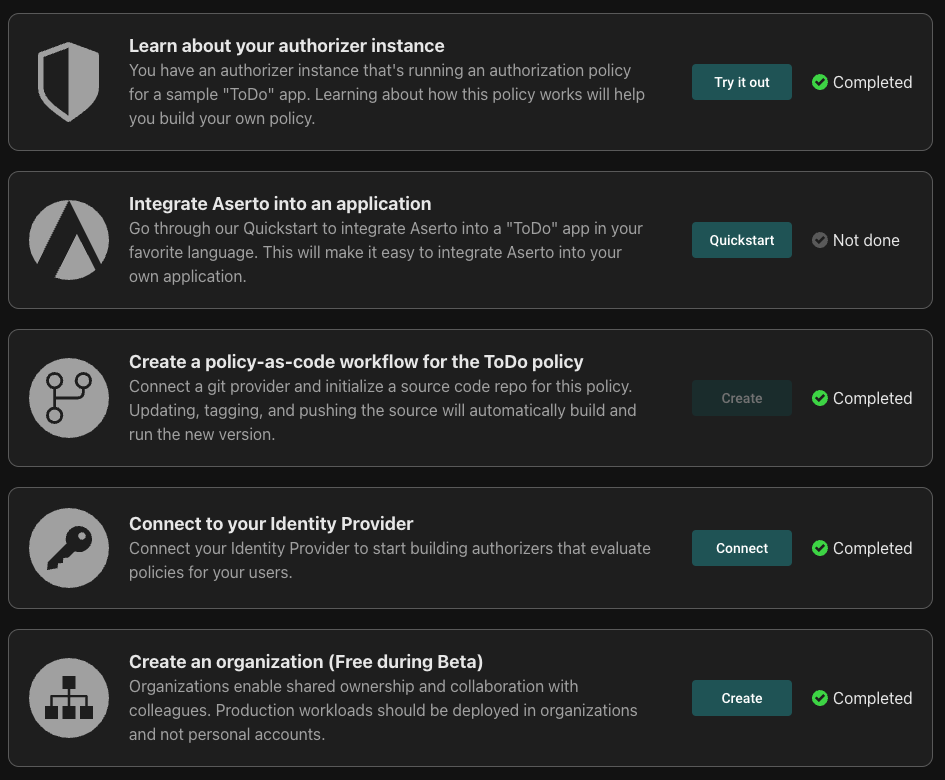
Existing users are not presented with the getting started experience as it requires creating some resources in a user's account. See our documentation for information on how to enable Getting Started.
Images
The Registry tab was replaced with Images and now gives visibility across images from any connected Policy Registry including OPCR.io, GHCR.io and GitLab. By default, all accounts are connected to Aserto’s built-in Container Registry for that tenant (Aserto Policy Registry) as well as the Aserto Public Policy Registry which hosts our sample policy images. Users can then add additional Policy Registry connections to get visibility into other registries.
The Aserto Policy Registry contains the same images as the previous `Registry` tab. The Aserto Public Policy Images registry is managed directly by Aserto and is read-only, while other registries are read/write.
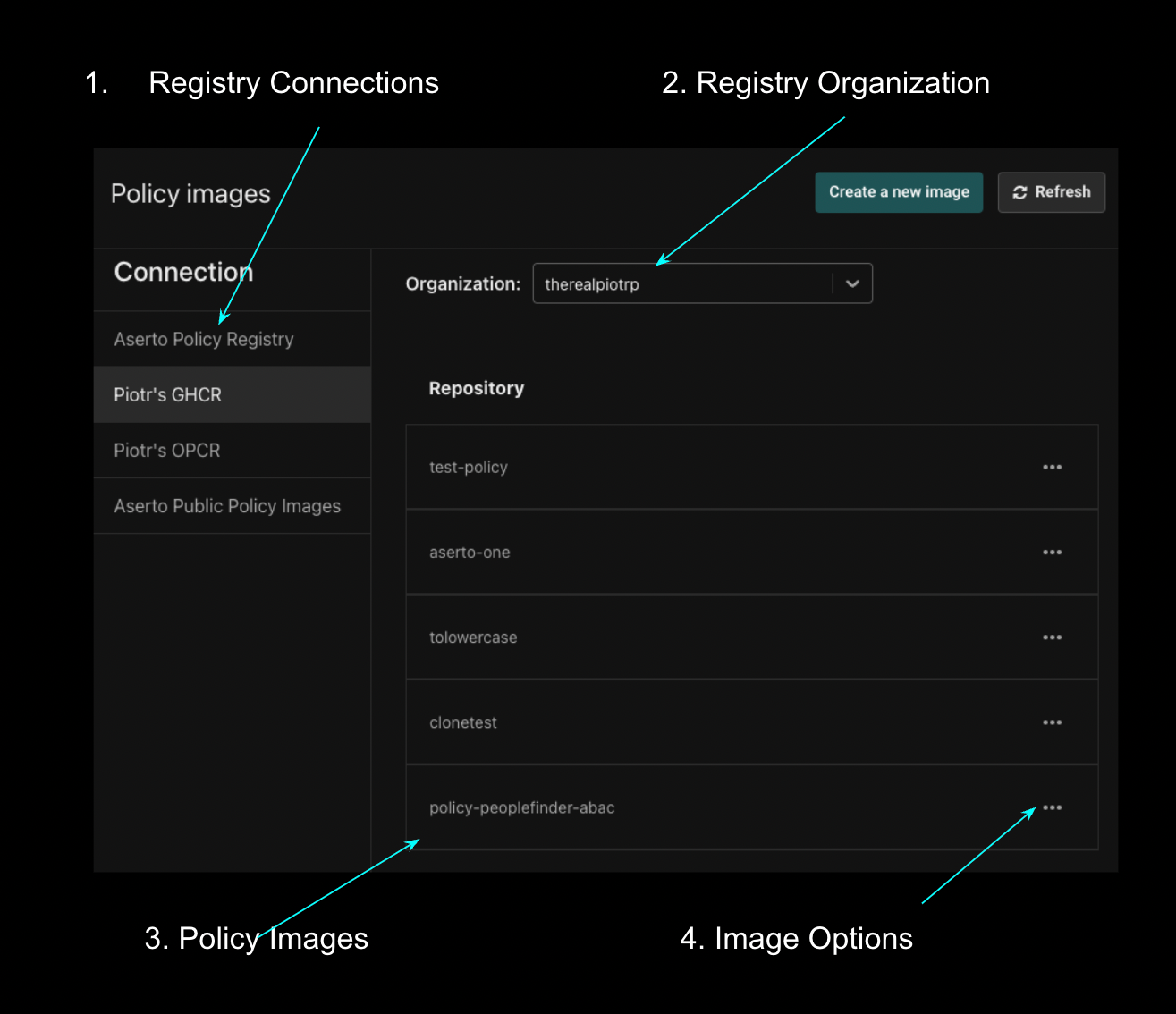
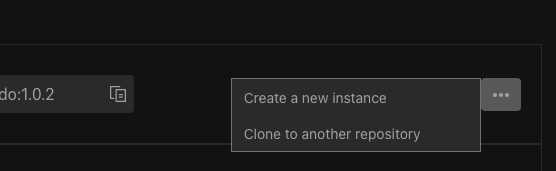
Image details
The Image Details view now provides a menu for each digest. That menu enables users to either clone a digest into their Aserto Policy Registry, making it mutable, or to create a Policy Instance directly from that digest. This makes it much easier to manage policies directly from the console.
Policy instance
We’ve added several new features to the policy instance view:
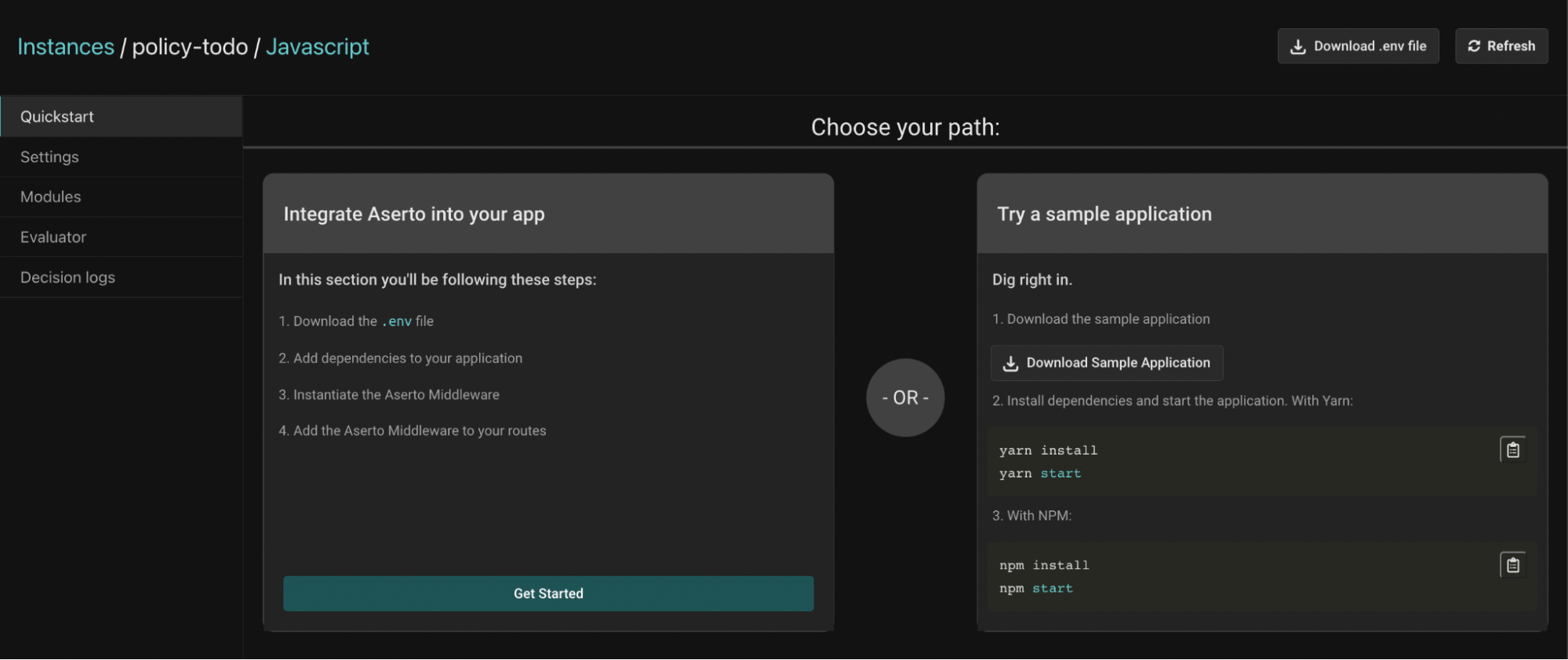
Quickstarts
We have added language-specific guides which shorten the time it takes to use the policy instance in your application.
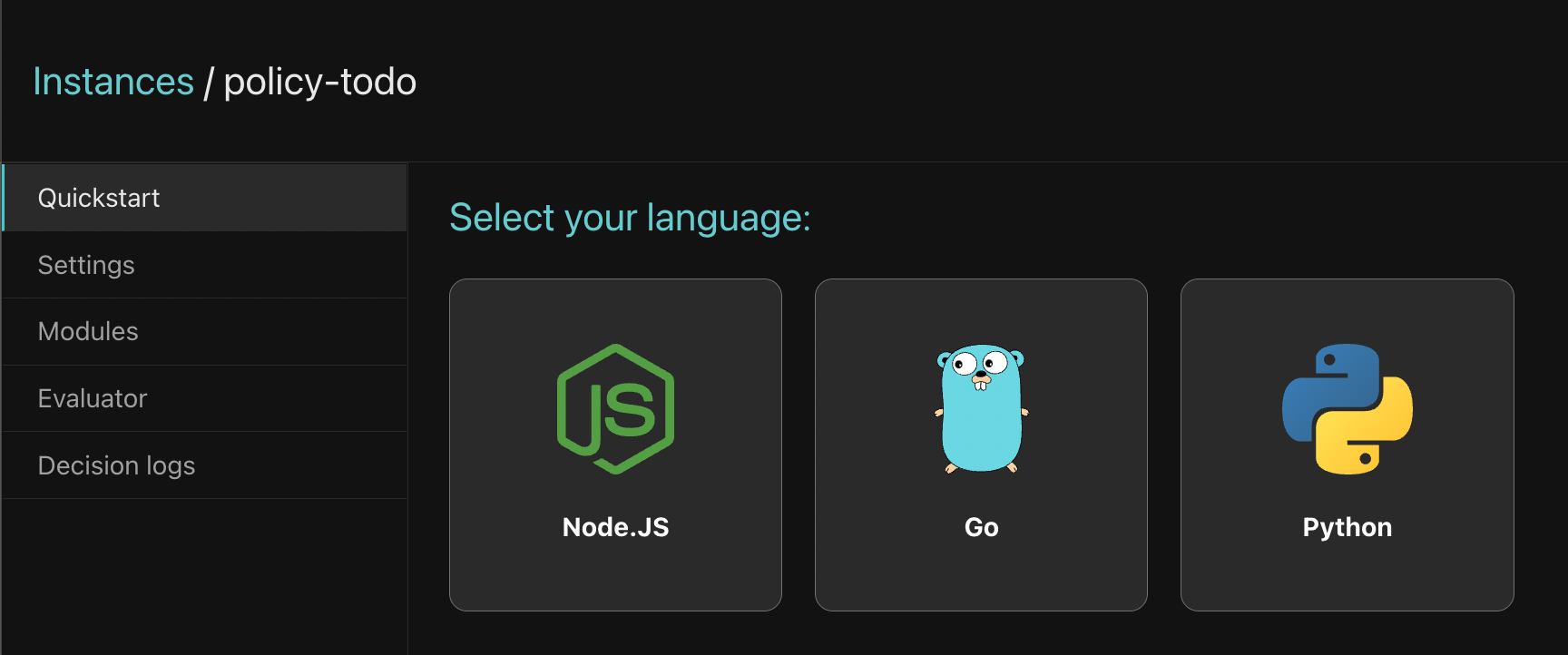
After selecting the language of your choice, you can choose to follow a step-by-step guide for adding the Aserto SDK to your application. Alternatively, you can download a sample application in your language of choice, which includes everything you’d need to get started.
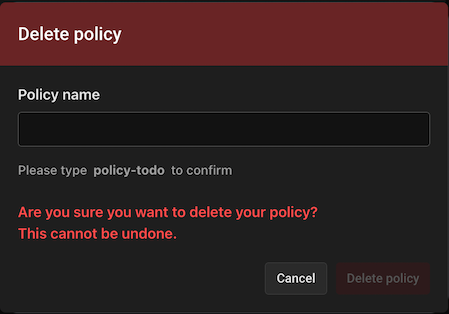
Deleting policies
To ensure policy instances are not deleted in error, we’ve added a safety mechanism that requires that you type the policy instance name before you can delete the policy instance. You can access the “Delete policy” button at the bottom of the policy instance’s settings tab.
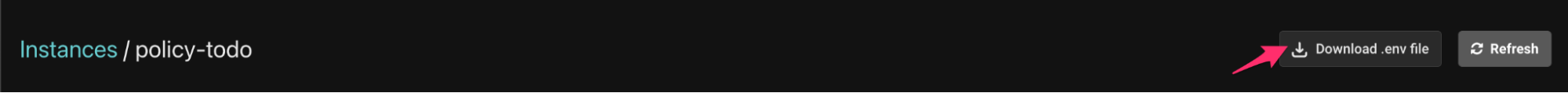
Download .env file in Policy Instance settings
Instead of having to copy credentials from the policy instance settings page, you can now download a `.env` file for the policy instance. It will include your policy ID, tenant ID and authorizer API key, which are required by the Aserto SDK.
Policy evaluator
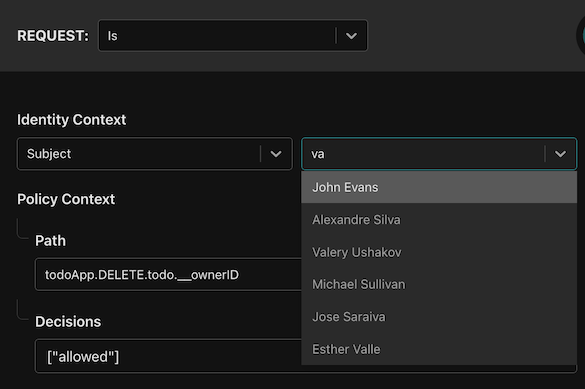
To make it easier to use the policy evaluator, you can now select any user from your directory after selecting the “subject” option in the evaluator (instead of providing an email address or a JWT).
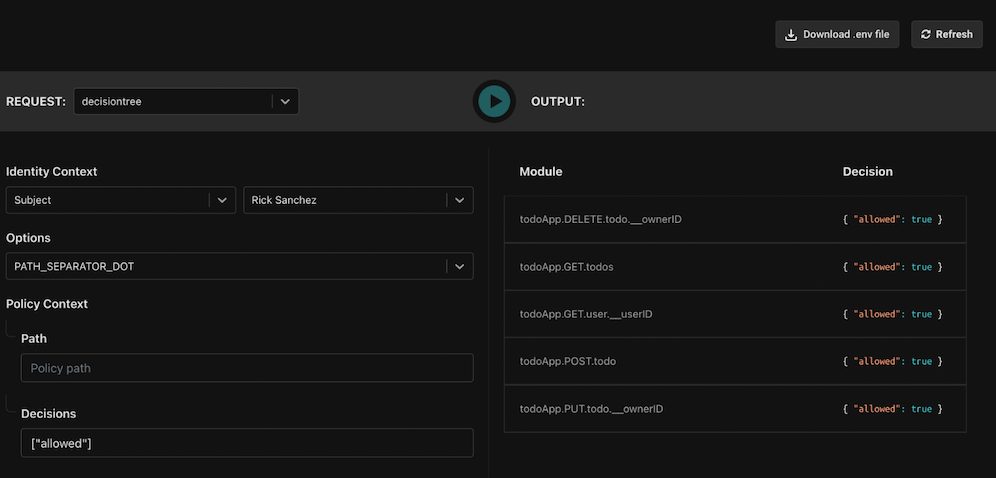
To make it easier to view the decision tree, we now render all of the decisions as a table:
Additional improvements
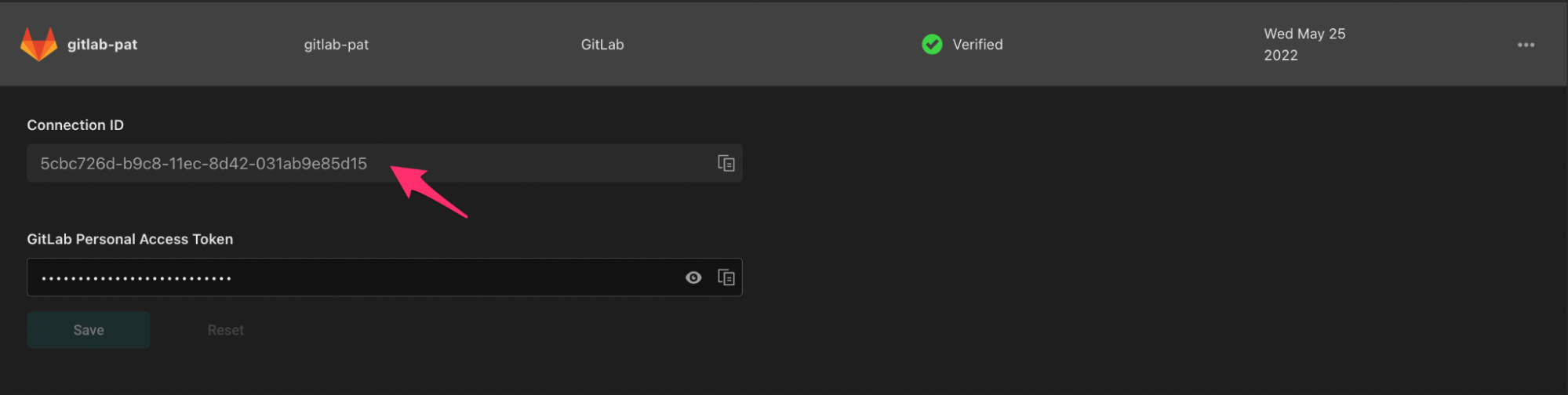
Expose connection ID
All connections now list their Connection ID directly on the Connections tab.
Scale enhancements
Large datasets, including registries with many Policy Images and images with many digests, now stream in data as needed to give users better access to their resources.
Screen size enhancements
We’ve made improvements to UI rendering on screens as small as tablets.
Tell us what you think!
We'd love to hear your thoughts about these updates, as well as any other questions you may have. Join our Slack channel today, we'd love to hear from you.

Piotr Puszkiewicz
Principal Software Engineer

Roie Schwaber-Cohen
Developer Advocate
Related Content

mage-loot: Dependency management for Go
In this post, we review mage-loot, an open-source utility package that includes dependency management and other helpful utilities for managing projects built with mage.
Jun 9th, 2022

Adding Authorization to A Node.js Application
In this tutorial, we'll learn how to add authorization to a Todo app written in Node.js, using the Aserto Express.js middleware.
Jun 30th, 2022

Adding Authorization to A Python Application
In this tutorial, we'll learn how to add authorization to a Todo app written in Python, using the Aserto Python middleware.
Jul 21st, 2022
&color=rgb(100%2C100%2C100)&link=https%3A%2F%2Fgithub.com%2Faserto-dev%2Ftopaz)